ESET researchers discovered a malware family with tools that show signs they’re used in targeted attacks.
ESET researchers have discovered a previously unknown malware family that utilizes custom and well-designed modules, targeting operating systems running Linux. Modules used by this malware family, which we dubbed FontOnLake, are constantly under development and provide remote access to the operators, collect credentials, and serve as a proxy server. In this blogpost, we summarize the findings published in full in our white paper.
To collect data (for instance ssh credentials) or conduct other malicious activity, this malware family uses modified legitimate binaries that are adjusted to load further components. In fact, to conceal its existence, FontOnLake’s presence is always accompanied by a rootkit. These binaries such as cat, kill or sshd are commonly used on Linux systems and can additionally serve as a persistence mechanism.
The sneaky nature of FontOnLake’s tools in combination with advanced design and low prevalence suggest that they are used in targeted attacks.
The first known file of this malware family appeared on VirusTotal last May and other samples were uploaded throughout the year. The location of the C&C server and the countries from which the samples were uploaded to VirusTotal might indicate that its targets include Southeast Asia.
We believe that FontOnLake’s operators are particularly cautious since almost all samples seen use unique C&C servers with varying non-standard ports. The authors use mostly C/C++ and various third-party libraries such as Boost, Poco, or Protobuf. None of the C&C servers used in samples uploaded to VirusTotal were active at the time of writing – which indicates that they could have been disabled due to the upload.
Known components of FontOnLake
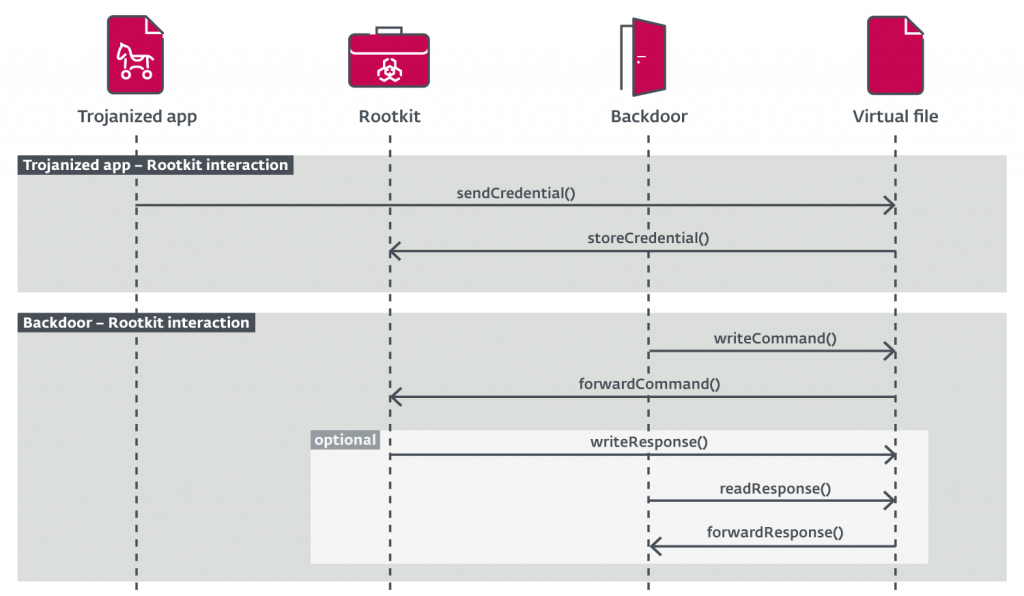
FontOnLake’s currently known components can be divided into three following groups that interact with each other:
- Trojanized applications – modified legitimate binaries that are adjusted to load further components, collect data, or conduct other malicious activities.
- Backdoors – user mode components serving as the main point of communication for its operators.
- Rootkits – kernel mode components that mostly hide and disguise their presence, assist with updates, or provide fallback backdoors.
Trojanized applications
We discovered multiple trojanized applications; they are used mostly to load custom backdoor or rootkit modules. Aside from that, they can also collect sensitive data. Patches of the applications are most likely applied on the source code level, which indicates that the applications must have been compiled and replaced the original ones.
All the trojanized files are standard Linux utilities and each serves as a persistence method because they are commonly executed on system start-up. The initial way in which these trojanized applications get to their victims is not known.
Communication of a trojanized application with its rootkit runs through a virtual file, which is created and managed by the rootkit. As illustrated in Figure 1, data can be read/written from/to the virtual file and exported with its backdoor component upon the operator’s request.
Backdoors
The three different backdoors we discovered are written in C++ and all use, albeit in slightly different ways, the same Asio library from Boost for asynchronous network and low-level I/O. Poco , Protobuf, and features from STL such as smart pointers are used as well. What is rare for malware is the fact that these backdoors also feature a number of software design patterns.
The functionality that they all have in common is that each exfiltrates collected credentials and its bash command history to its C&C.
Considering some of the overlapping functionality, most likely these different backdoors are not used together on one compromised system.
All the backdoors additionally use custom heartbeat commands sent and received periodically to keep the connection alive.
The overall functionality of these backdoors consists of the following methods:
- Exfiltrating the collected data
- Creating a bridge between a custom ssh server running locally and its C&C
- Manipulating files (for instance, upload/download, create/delete, directory listing, modify attributes, and so on)
- Serving as a proxy
- Executing arbitrary shell commands and python scripts
Rootkit
We discovered two marginally different versions of the rootkit, used only one at a time, in each of the three backdoors. There are significant differences between those two rootkits, however, certain aspects of them overlap. Even though the rootkit versions are based on the suterusu open-source project, they contain several of their exclusive, custom techniques.
Combined functionality of the two versions of the rootkit we discovered include:
- Process hiding
- File hiding
- Hiding itself
- Hiding network connections
- Exposing the collected credentials to its backdoor
- Performing port forwarding
- Magic packets reception (magic packets are specially crafted packets that can instruct the rootkit to download and execute another backdoor)
Following our discovery while finalizing our white paper on this topic, vendors such as Tencent Security Response Center, Avast and Lacework Labs published their research on what appears to be the same malware.
All known components of FontOnLake are detected by ESET products as Linux/FontOnLake. Companies or individuals who want to protect their Linux endpoints or servers from this threat should use a multilayered security product and an updated version of their Linux distribution; some of the samples we have analyzed were created specifically for CentOS and Debian.
In the past we described an operation that shared certain behavioral patterns with FontOnLake; however, its scale and impact were much bigger. We dubbed it Operation Windigo and you can find more information about it in this white paper and this follow-up blogpost.
Additional technical details on FontOnLake can be found in our comprehensive white paper.
Author : Vladislav Hrčka (AVAR 2021 Virtual Speaker)
Company: ESET
Comments are closed.